The FBI says that computer hackers accessed, and in one case stole, voter registration files in two states, potentially compromising personal information and putting crucial election data at risk just three months before voters head to the polls.
And if that weren’t unsettling enough, the techniques that the hackers used were neither sophisticated nor particularly hard to employ, proving that it’s not just high-end hackers from foreign governments, like the ones believed to be targeting U.S. political organizations, that elections officials need to worry about in the runup to November.
“I don’t think anyone can assume that these vulnerabilities would be unique to these states,” Pamela Smith, the president of Verified Voting, a nonprofit group that advocates transparency and security in U.S. elections, told The Daily Beast. “This is a time when assuming is not the best thing to do.”
The FBI’s analysis of the hacks, contained in a security alert first reported by Yahoo News, shows that Arizona’s elections website was penetrated in June using a common vulnerability that’s well known to security experts. Then, in July, Illinois’ voter files were accessed apparently using stolen login credentials, which could have been obtained by spear phishing a state employee. (The FBI didn’t identify the victims by name in the alert, but experts familiar with the cases pointed out that they match reported hacks in Arizona and Illinois, where officials have acknowledged the intrusions.)
On the scale of hacker sophistication, these attacks rank on the low-end, relative child’s play for the kinds of skilled operators that U.S. officials suspect may have stolen emails from the Democratic National Committee and Democrat and Republican lawmakers in an attempt to sow chaos in the presidential elections. There’s no hard evidence yet that the same crew, believed to be working for the Russian government, was at work in the states. But the hacks underscore that these states and others present easy targets. Experts predicted that Arizona and Illinois won't turn out to be the only victims.
“I think it’s fair to say there are more states out there that have been hacked and don’t know it, or that are being hacked and are trying to deal with it quietly,” David Heyman, a former assistant secretary at the Homeland Security Department, told The Daily Beast.
For the past few weeks, the Homeland Security Department and computer security experts have been warning state and local elections officials to be on special alert for hackers targeting voting systems, including electronic voting booths, tabulating machines, and voter registration files that are stored online. The attacks on Arizona and Illinois suggest that officials’ concerns were well-founded.
“This is serious,” Heyman said. “Actual tampering of voter registration files, or even the prospect of tampering, can very well put in question the integrity of the election. And in an election where some are already questioning if the system is rigged, this could easily undermine confidence in the system, or worse, sow doubt in actual election results and weaken the ability for a winning candidate to govern.”
Heyman and other experts noted that hackers don’t need to actually hijack a voting machine or alter ballot-counting software to undermine confidence in election results. Merely the credible claim that an election had been tinkered with could compel a candidate’s supporters to cry foul.
And one candidate, of course, already is. Republican nominee Donald Trump has said that the only way he’ll lose in some key states if the election is “rigged,” by forces he didn’t name. The now instances of election-related hacking could fuel Trump’s suspicions that vote rigging is real.
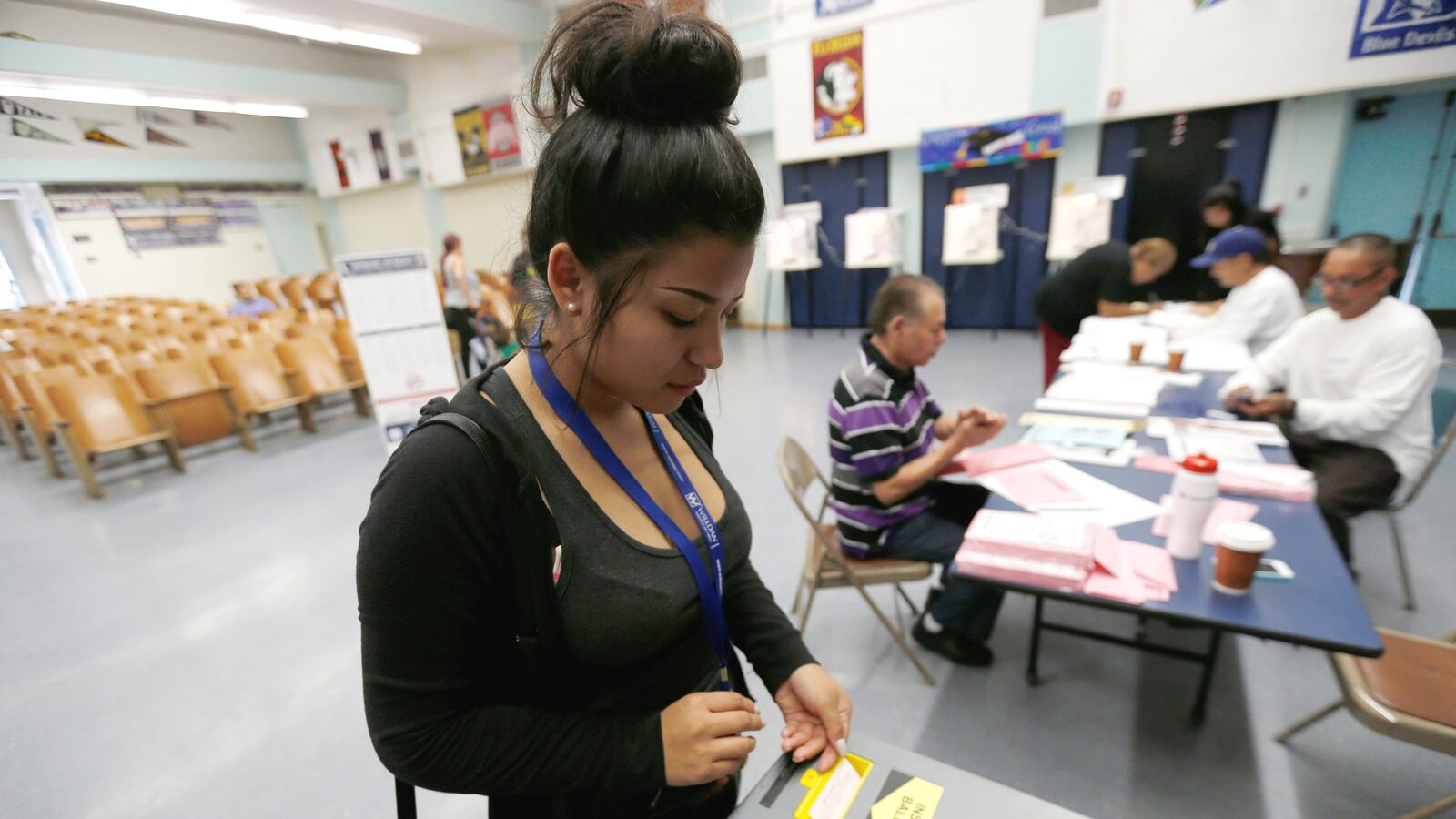
How could hackers use voter registration files to disrupt Election Day? The most worrisome scenario, experts said, would be if voters’ names were erased from the rolls, so that when they showed up to vote, there was no proof they’d ever registered.
“That could cause long lines, and people might have to cast provisional ballots,” which aren’t counted right away, Michael McDonald, an associate professor at the University of Florida and an expert on voting systems, told The Daily Beast.
Changing or deleting voter information is the “most severe” threat to such records, Smith said. States vary in their rules about who can cast a provisional ballot, and some of them don’t allow a voter to cast a choice in every race, she noted. Counting those ballots requires more work that could delay reporting the results, Smith said.
There's no indication that the voter records in Arizona or Illinois were deleted or altered. But anecdotal evidence of problems with voter registration files has been circulating for months.
During the primary election in Arizona, for instance, a number of voters found that their party affiliation had been changed without their knowledge. When they showed up to vote in the state’s closed primary elections, some were told they were ineligible to vote with the party of their choice.
State officials have blamed the problem at least in part on an error at the state’s driver registration bureau. But similar problems have reportedly cropped up in California, Connecticut, Maryland, New York, and Pennsylvania.
If states have back up files on all registered voters, they should be able to recover from even a severe attack on the voter files.
“It should be possible to go back and recreate the data if there was any suspicious activity on the data itself,” McDonald said.
And most states are doing that. “The states take nightly backups of the voter registration data,” Matthew Masterson, a commissioner with the U.S. Election Assistance Commission, told The Daily Beast. The commission, which was set up after the 2000 presidential election recount in Florida, helps states test the security of voting technology. Masterson said that he thought “most states” were probably aware of the problems in Arizona and Illinois and have taken additional steps to secure their voter files.
But backing up those files, if they were deleted or altered, would take time, and in the frenzy of Election Day, the damage to public confidence might be harder to repair.
State officials are bracing for potential trouble. On August 15, the Homeland Security Department held a conference call with state elections officials after they said they wanted more guidance from the federal government about how to protect elections systems. State officials haven’t received any specific recommendations since that call, Kay Stimson, a spokesperson for the National Association of Secretaries of State, told The Daily Beast.
The department has offered to help states assess their security vulnerabilities and perform scans of networks to look for weak points or intrusions that have already occurred. But Stimson said it’s not clear who will pick up the tab or provide the labor for that effort.
“There was no real detailed discussion about how a scan would work or who would come and what resources are involved,” Stimson said.
But with the elections practically around the corner, it’s not clear what the states that haven’t put strong security procedures in place could do to ward off mischief, even if the feds pitched in to help.