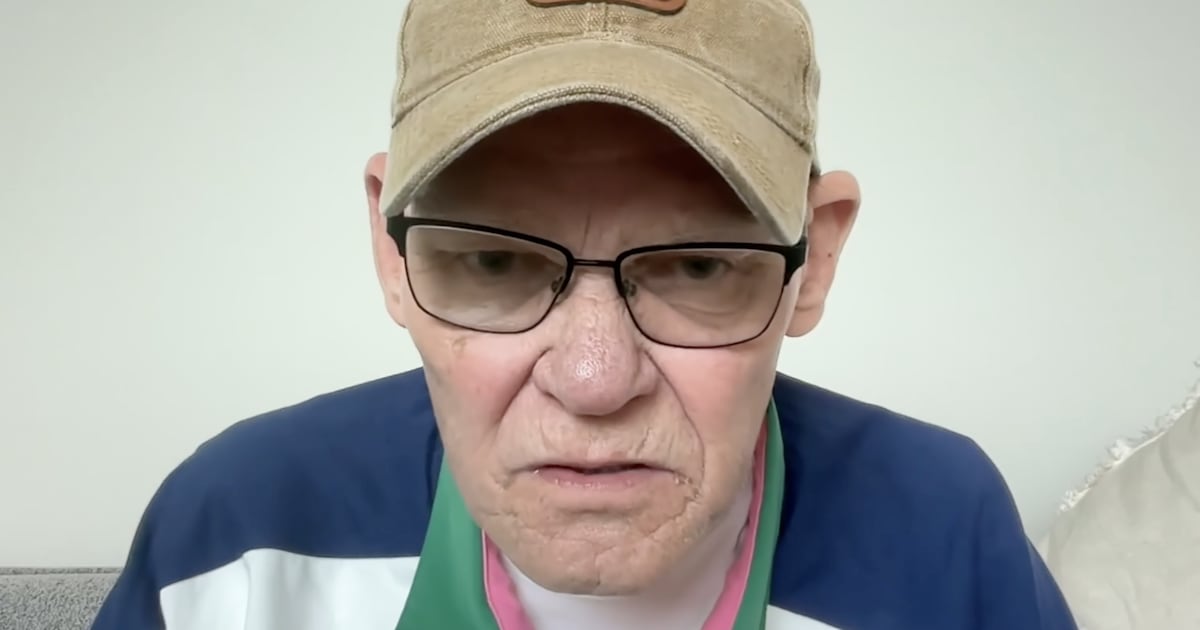
Nicholas Burks likes games of chance. In fact, he’s so keen on gambling he’s been running a sweepstakes site, Raffle of the Day, according to the FBI. And according to the Raffle of the Day’s Instagram, the offerings up for grabs have included Rolex watches, PlayStation 5s, even cars like a Chevrolet Corvette and a Dodge Charger.
But Burks appears to have taken one big chance that didn’t pay off: gambling the FBI wouldn’t find out he allegedly stole data from his old employers and then, posing as an anonymous ransomware hacker, extorted them out of $300,000.
It all started when Tennessee-based tech support firm Asurion fired Burks for performance-related reasons. Upon his exit, he surreptitiously stole a company laptop, according to court records obtained by The Daily Beast. According to his indictment, which was unsealed just this month, Burks allegedly later used the laptop to download sensitive internal corporate information. He got in touch with company executives listing the data he stole—including employee social security numbers, banking information, as well as customers’ names and addresses—and proceeded to demand a ransom.
He threatened that, if he didn’t receive hundreds of thousands of dollars within 24 hours, he would publish the stolen data, according to court records.
The company paid up—$300,000 in cryptocurrency—and Burks decided to make off with the money and buy himself a Mercedes Benz, court documents state. He allegedly used several cryptocurrencies and a tumbler, a kind of service that helps to anonymize cryptocurrencies and their origins, to receive the funds, eventually redistributing them to several other accounts, including ones associated with businesses he owns, like Raffle of the Day, the filings note.
The feds have since seized Burks’ “raffle” website, alerting those who want to participate in the raffles, or those that have in the past, that they’ve likely been victims of fraud. (In recent months, the Raffle of the Day Instagram has advertised its services by claiming Nick can teach people “how to make 7-figures” and how to “start and scale your very own business”—which all screams of legitimacy.)
Burks, 29, has also been arrested, according to court filings.

But along the way, Asurion wasn’t operating alone. It turns out some of the company’s payment to Burks was orchestrated alongside law enforcement.
Asurion confirmed to The Daily Beast that it teamed up with federal authorities to help nab Burks, noting they worked with law enforcement on the case.
“We worked closely with law enforcement from the beginning and throughout the event, including with respect to payments made to Burks,” an Asurion spokesperson told The Daily Beast.
While the company declined to provide additional details on their cooperation with law enforcement, a 2019 federal search warrant application laid out some of the contours of the collaboration and efforts to snuff out Burks’ scheme. Asurion began paying $50,000 to the extortionist while launching an internal investigation and contacting the FBI—an investigation which included watching Burks as Asurion paid him a $5,000 installment, according to a news report from a local paper, The Tennessean.
“Because of the ongoing criminal prosecution of Burks, we are limited in the information we can share, but it’s important to underscore that there was no impact to customer, employee or other company information as a result of Burk’s [sic] actions.” Asurion added.
A lawyer assigned to Burks’ case, and Burks himself, did not respond to requests for comment. The U.S. Attorney’s Office in the Middle District of Tennessee, which is prosecuting the case, declined to comment.
This bizarre case is just the latest instance of company insiders lashing out, stealing sensitive internal data, and then demanding ransoms pretending to be ransomware hackers extorting companies for millions.
In January of this year, another “Nicholas”—Nickolas Sharp—used credentials he was given as part of his job, stole gigabytes of confidential data, and then sent an email to leadership at his firm threatening to publish the stolen data unless the company paid him approximately $2 million, according to an indictment unsealed this month. The firm in question is suspected to be New York-based tech company Ubiquiti.
When the company didn’t pay the ransom, Sharp released some of the stolen data, according to court documents. After the FBI raided his home, Sharp allegedly later posed as a whistleblower and got in touch with media outlets to try to further his cause and cover up his situation, claiming the theft wasn’t an insider, but rather an external hacker that found a vulnerability in the company’s computer systems.
For Burks, his chapter on dealing with law enforcement isn’t over just yet. While he was arrested in Georgia and released on bond pending his trial, the criminal prosecution is ongoing. While his raffle site has been seized, the sweepstakes apparent Facebook, YouTube, and Instagram accounts are still accessible.