Iranian hackers posing as American job recruiters targeted nearly 200 American and European defense industry employees in a campaign disrupted by Facebook security.
In a press conference on Thursday, Facebook security officials linked the effort to a shadowy group of hackers known in the cybersecurity industry as “Tortoiseshell.” Researchers had previously documented Tortoiseshell targeting IT systems in Saudi Arabia and U.S. military veterans using similar techniques.
The focus on Western defense and aerospace industry targets marked what Facebook called a “significant expansion” of the group’s focus.
In order to gain access to their targets, Tortoiseshell hackers “deployed sophisticated fake online personas to contact its targets and build trust and trick them into clicking on malicious links.”
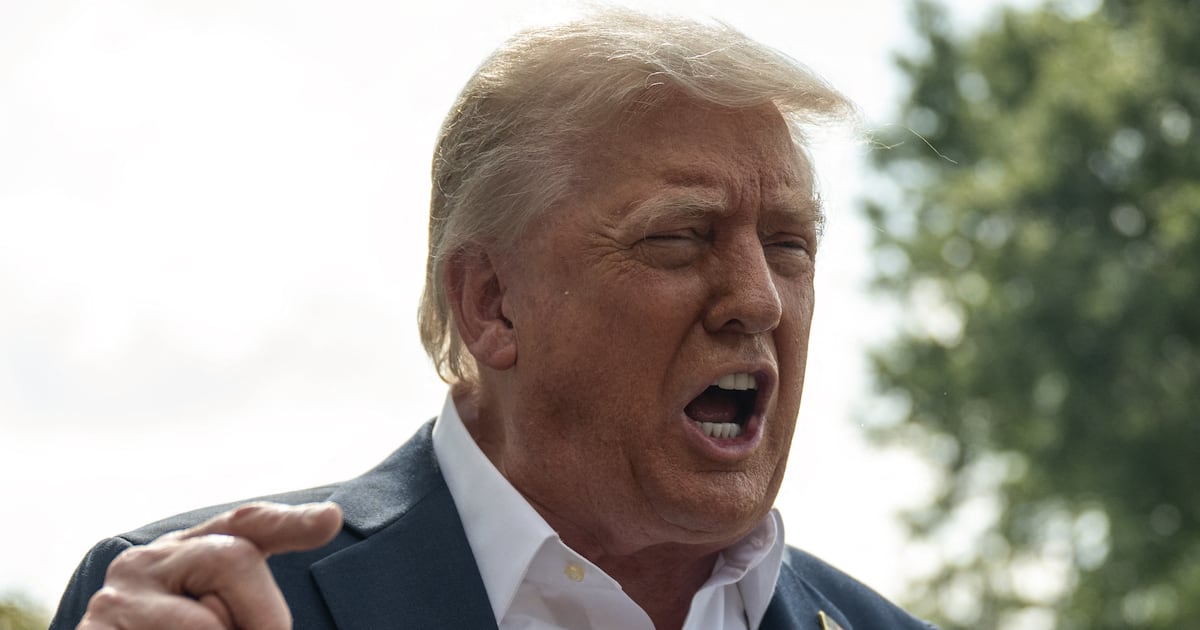
Tortoiseshell personas impersonated employees in a variety of industries from hospitality and tourism to defense contractors. A list of websites used in the campaign, published by Facebook to warn potential victims, includes a number of domains meant to spoof legitimate defense industry sites Lockheed Martin and media outlets like CNN. The hackers also appear to have used websites crafted to look like part of the Trump family and business empire, including one site for the “Eric Trump Foundation.”
Americans were foremost among the targets of the Tortoiseshell campaign but Facebook also found defense and aerospace industry employees in Europe and the U.K. in the group’s crosshairs.
While Tortoiseshell is believed to be based in Iran, it’s unclear yet whether the group has links to the Iranian government. Despite its murky associations and origins, security researchers for the platform were able to link the group to custom malware developed by an Iranian firm Mahak Rayan Afraz, a firm linked to Iran’s Islamic Revolutionary Guard Corps with “current and former MRA executives have links to companies sanctioned by the US government,” according to Facebook.