“Personal data of veterans Ukrainian ATO,” one of the tweets, before linking to a cache of allegedly hacked data, published Thursday reads.
“Tomorrow more,” the account, apparently belonging to Aric Toler, a researcher at open-source intelligence and journalism community Bellingcat, promised. “It will be a sensation, really,” the tweet added.
Except this account, even though it pictures Toler in his messy short hair and brown glasses, does not really belong to the researcher, or even Bellingcat more generally. Instead, this account and a series of others that tweeted similar material throughout the week appears to be part of campaign to discredit Bellingcat, an organization that has repeatedly irked the Russian government and military with well-sourced reports into the MH17 downing. The campaign, although using only a relatively small accounts and fairly crude in sophistication, shows how disinformation trolls may sometimes not just dump allegedly hacked data to harm the actual hacking victim, but also spin it in such a way to have a knock-on effect on other targets, too.
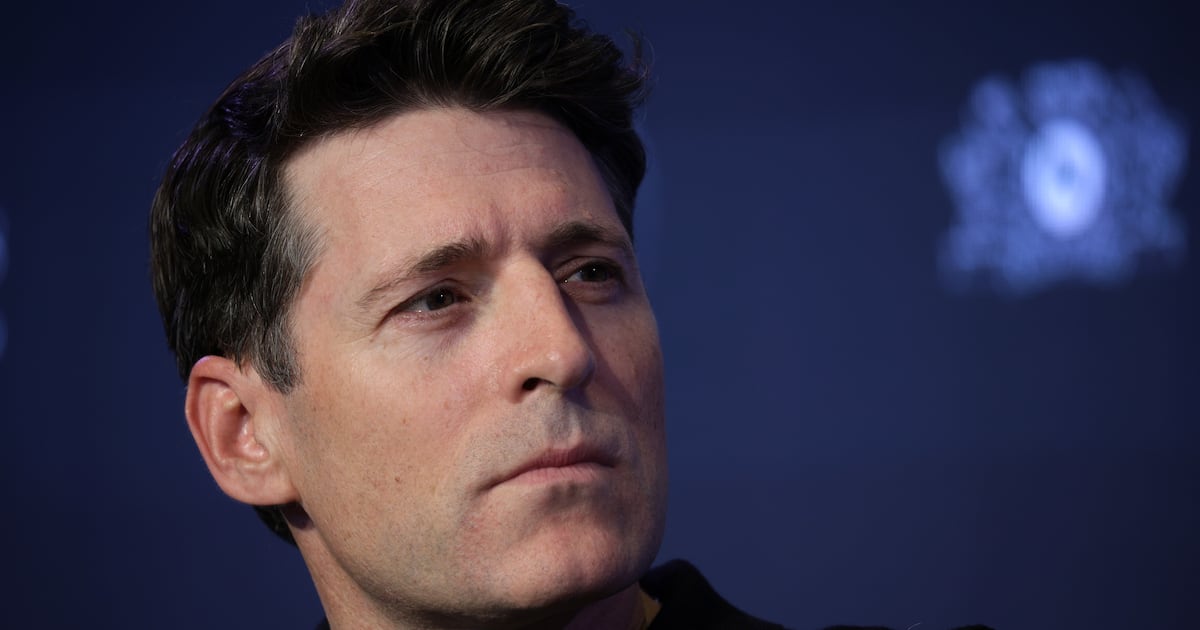
“We’ve nothing to do with the account and not sure why they’d bring us into what they’re doing, maybe to smear us in the eyes of the Ukrainian public,” Eliot Higgins, the founder of Bellingcat, told The Daily Beast, referring to another account that was claiming association with the organization.
That second account appears to be the epicenter of this smearing mission. “Welcome to the official Anonymous Poland Twitter! Researcher and hacker at @bellingcat,” the account’s Twitter bio reads.
As Ben Nimmo, a researcher with a focus on social-media disinformation campaigns from the Atlantic Council’s DFRLab, pointed out on Twitter, this ‘Anonymous Poland’ account was created back in 2012, and started posting this fall. It previously retweeted gambling, VPN, and knives advertisements, resembling a more generic, marketing-focused bot. (On Friday, Anonymous Poland shut down its account.)
Several other accounts that attempted to push the material had similar histories of banal marketing tweets before being repurposed for political ends, according to a set of related tweets that The Daily Beast archived. Many of these accounts do not appear to have been created for the sole purpose of spreading disinformation. Instead, it seems they were hijacked from their real owners; one belongs to a real family-law and criminal-defense law firm. That account hasn’t tweeted about legal issues since 2016, and only sprung back up with these latest data dumps.
Many of the accounts also deliberately tweeted their caches of data directly at journalists from various media outlets. The law-firm account, for instance, tweeted at several BBC reporters and Fox News’s Sean Hannity. One account used the CNN logo as its Twitter avatar, perhaps in a sloppy attempt to appear more legitimate.
That style of flagging data to journalists has a startling resemblance to other accounts that have popped up before. In July 2016, an account called “Ukraine.info” tweeted news of alleged secret, biological tests in the country, before another dubbed “W-News” joined in and tweeted apparently sensitive documents, Motherboard reported at the time. Clearly W-News, like some of the accounts in the new Bellingcat case, were trying to pose as journalists, even if in a very unconvincing way—W-News used a photo of reporter and comedian Katherine Timpf as its avatar. Accounts in this summer 2016 campaign also tweeted their caches of files and data at a bevy of journalists, just like the accounts trying to discredit Bellingcat.
Following that brief spasm of activity, an account claiming to be from Anonymous Poland posted tweets declaring it had hacked data from U.S. charity the Bradley Foundation, a November 2016 report from cybersecurity firm Digital Shadows recalls. The firm found more than 8,000 nearly identical tweets posted by some 7,500 Twitter accounts, the report adds. Crucially, that same month Vocativ found that although the Bradley Foundation hack was real, the data dump included a fake $156 million check to Hillary Clinton, highlighting how the bot’s apparent purpose was discreditation and misinformation, rather than just spreading hacked data.
In 2016 cybersecurity company ThreatConnect said in a report that it believed Anonymous Poland was linked to Russian hackers, in part because the group tweeted data stolen from the World Anti-Doping Association (WADA). Cyberattacks on the WADA are widely believed to be the work of hackers sponsored by Russia.
In his March 2017 testimony before the Senate Select Committee on Intelligence, Thomas Rid, an academic who has closely followed Russian disinformation campaigns, put Anonymous Poland in the same bucket as other groups linked to Russia’s military or foreign-intelligence agency GRU—such as Guccifer 2.0 or DC Leaks. Other researchers have also attributed the Anonymous Poland Twitter presence to APT28, otherwise known as the Russian hacking group Fancy Bear.
“What may be going on here is this: Bellingcat has been targeted by APT28 for a while, and the researchers know it. Using the already APT28-linked ‘Anonymous Poland’ moniker enables sending a hidden message of intimidation on a public channel: Bellingcat get the message; but most people won’t. And most journalists and researchers likely won’t comment because the evidence is too flimsy. Respect, I say, a very nimble tactic,” Rid, who is now professor of strategic studies at Johns Hopkins University, told The Daily Beast.
It is not totally clear who exactly is behind this latest campaign, although it does appear to be related to the earlier Anonymous Poland and Ukraine.info ones, at least in approach and intended targets.
Bellingcat has previously shown how Russia may have inadvertently provided the best evidence yet that the Syrian government is responsible for chemical-weapons attacks; examined Russian airstrike footage showing potential targeting of first responders; and traced the movements of the Russian Buk missile launcher that downed Flight MH17.
At least one of the caches pushed by this fake Bellingcat and other accounts includes around 100MB of Word documents, spreadsheets, and images.
Twitter, it seems, did react pretty swiftly in limiting access to the offending tweets, though. After several open-source researchers tweeted about the suspicious accounts, it was not possible to find related tweets through Twitter’s ordinary search function. The accounts themselves were accessible to searchers who knew the exact username.
A number of the service providers hosting the allegedly hacked data also responded fairly quickly. The MEGA link Anonymous Poland posted was already down on Thursday, as was at least one of the caches hosted on a service called SendSpace. These files may have been taken down because members of the open-source research community reported the disinformation campaign and hosted data to SendSpace.
“Please check,” many of the accounts incessantly tweeted to reporters and other media personalities Thursday.