While Google weighs exiting China, a classified FBI report says that country has already developed a massive cyber army attacking the U.S. with “WMD-like” destruction capabilities.
A classified FBI report indicates that China has secretly developed an army of 180,000 cyberspies that “poses the largest single threat to the United States for cyberterrorism and has the potential to destroy vital infrastructure, interrupt banking and commerce, and compromise sensitive military and defense databases."
These spies are already launching 90,000 attacks a year just against U.S. Defense Department computers, according to a senior FBI analyst familiar with the contents of the report, making news Tuesday that the Chinese government may have hacked the email accountings of human-rights activists, prompting Google to consider withdrawing from that country, seem like child’s play.
The FBI report estimates that the Chinese Army has developed a network of over 30,000 Chinese military cyberspies, plus 150,000 private-sector computer experts, whose mission is to steal American military and technological secrets.
• Douglas Rushkoff: The Great Google Coverup? Cyber warfare is part of every developed country's 21st century arsenal. Although no U.S. official will admit it, the Pentagon, CIA, and NSA regularly probe and try to hack into China's military and industrial computer networks to obtain the information that years ago were brought back by the James Bonds of spy services. The U.S., and many of our European allies, try to find ways to wreck some havoc in the Chinese computer grid if a conflict ever takes place. The difference is that the Chinese are better than anyone else and lead the way in technological breakthroughs for the cyber battlefield. The FBI report concludes that a massive Chinese cyberattack could “be in the magnitude of a weapon of mass destruction," says the analyst, who requested anonymity because he was not authorized to speak about it, adding that it would do substantial damage to the American economy, telecommunications, electric power grid, and military preparedness.
The FBI report estimates that since 2003, the Chinese Army has specifically developed a network of over 30,000 Chinese military cyberspies, plus more than 150,000 private-sector computer experts, whose mission is to steal American military and technological secrets and cause mischief in government and financial services. China’s goal, says the FBI report, is to have the world’s premier “informationized armed forces” by 2020. According to the bureau’s classified information, the Chinese hackers are adept at implanting malicious computer code, and in 2009 companies in diverse industries such as oil and gas, banking, aerospace, and telecommunications encountered costly and at times debilitating problems with Chinese-implanted “malware.” The FBI analyst would not name the affected companies.
One of China’s most effective weapons, according to the FBI report, is a continuation of what Pentagon security investigators originally dubbed Titan Rain; it is a Chinese scanner program that probes national defense and high-tech industrial computer networks thousands of times a minute looking for vulnerabilities. The Chinese military hackers, the FBI analyst told me, enter without any keystroke errors, leave no digital fingerprints, and create a clean backdoor exit in under 20 minutes, feats considered capable only for a military or civilian spy agency of only a few governments.
These attacks are proliferating. The FBI report lays out the identifiable attacks originating from China just on the Defense Department computers; they increased from 44,000 in 2007 to 55,000 in 2008, and topped 90,000 last year. “They probe, they test our responses, as quick as we make changes and fix vulnerabilities, they are moving a step ahead,” the analyst told me.
The Chinese hackers aren’t after credit-card numbers or bank accounts or looking to steal private identities. Instead, they are hunting for information. Although the barrage of attacks may at times appear random, the FBI report concludes that it is part of a strategy to fully flush out U.S. military telecommunications and to better understand—and to attempt to intercept—intelligence being gathered by American spy agencies, particularly the National Security Agency.
“It’s the great irony of the Information Age that the very technologies that empower us to create and to build also empower those who would disrupt and destroy,” President Obama said last May when he announced a new White House office dedicated to protecting the nation’s computer systems. The Pentagon followed shortly after with a new military cyberspace command. In his remarks, the president said that, “In today’s world, acts of terror could come not only from a few extremists in suicide vests but from a few keystrokes of a computer.” And he admitted, “We’re not as prepared as we should be, as a government or as a country.”
China’s Ministry of Public Security has thousands of so-called Information Warfare Militia Units that effectively monitor all domestic Internet traffic of the country’s 140 million 'Net users. It’s this internal program that may have affected Google. On Tuesday, Google said it had detected a “highly sophisticated and targeted attack on our corporate infrastructure originating from China.” While Google did not specifically accuse the Chinese government, it said it was “no longer willing to continue censoring our results” on its Chinese search engine, as the government requires. Thus, it may need to withdraw from its largest potential market.
The private-sector issues affect government security. As a precondition to doing business in China, several years ago Microsoft was required to provide the government the source codes for the company’s Office software. The Chinese State Planning Commission contended that Microsoft's Windows operating system was a secret tool of the U.S. government and demanded Microsoft instruct Chinese software engineers on inserting their own software into Window's applications.
That gave the Chinese Army’s cyberwarfare department what computer hackers dub a “skeleton key,” allowing them access to almost every networked private business, military, and government computer in the U.S. Among the Chinese Army-backed Microsoft attacks, the FBI report includes successful forays against computer systems at the State Department, Commerce Department, the FBI, and the Naval War College, among others.
Some Chinese attacks plant embedded covert programs into government networks, searching for classified files and then automatically forwarding them by email to China. Using sophisticated “rootkit” programs to hide their presence, China’s hackers are “simply the most sophisticated,” says the senior FBI analyst. Homeland Security’s $1.8 billion computer network was penetrated by Chinese cyberwarriors in 2007, and an unknown amount of information was copied to a secure Chinese Web site. Even the Pentagon was breached in 2007 and again in early 2009, despite what it considered foolproof Titan Rain security patches. The 2009 intrusion was particularly worrisome since the Chinese managed to get inside the Pentagon's $300 billion Joint Strike Fighter project—the Defense Department's costliest weapons program ever—according to a government official familiar with the attack who spoke to The Daily Beast on the condition of anonymity. The cyber intruders copied several terabytes of data about the design and electronics systems, information that might make it easier to defend against the craft.
The FBI report concludes that many of the attacks identified as being from China might be part of Beijing’s plan to occasionally let its cyberspies be unmasked in order to give American and other Western counties a false sense of security. “There is no telling how many breaches there are that we haven’t yet picked up,” the FBI analyst told me. Most American government agencies have stopped buying Chinese hardware from Lenovo (the Chinese firm that acquired IBM's personal-computer division in 2005) and any software from the mainland.
But China is manufacturing microchips for dozens of major international companies, and those chips could hold viruses set to activate when used in a computer network. Chips employed in military applications could be designed to reverse engineer the weapon’s design and provide the information to Chinese spies. China’s microchip output is almost doubling every two years, and chip giant Intel has opened a multibillion-dollar plant in Dalian, China.
The FBI report’s grim conclusion: China sees its cyberwarriors as a critical component of its asymmetric warfare capability and the U.S. government should publicly identify China as an “ongoing intelligence risk.” The Chinese Embassy says that the country "opposes and forbids all forms of cyber crimes" and that charges of its cyber warrior program are remnants of “a Cold War mentality" and intended only “to fan up China threat sensations."
“Without confronting it as a major threat,” the FBI analyst told me, “companies like Google go to do business there incorrectly assuming they face no greater risk from Chinese penetrations than they face from any other country. It’s just not true. There’s no more imminent cyberthreat than the one posed by China.”
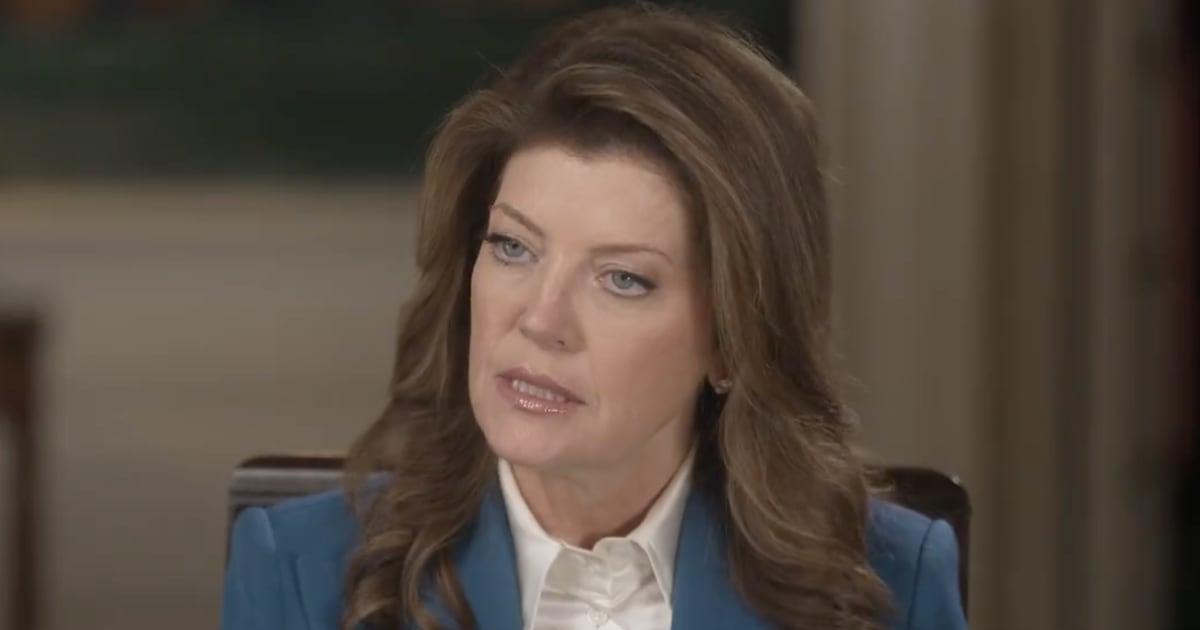
Gerald Posner is The Daily Beast's chief investigative reporter. He's the award-winning author of 10 investigative nonfiction bestsellers, on topics ranging from political assassinations, to Nazi war criminals, to 9/11, to terrorism. His latest book, Miami Babylon: Crime, Wealth and Power—A Dispatch from the Beach, was published in October. He lives in Miami Beach with his wife, the author Trisha Posner.